Page 1 :
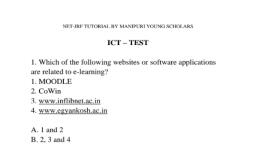
NET-JRF TUTORIAL BY MANIPURI YOUNG SCHOLARS, , ICT —- TEST, , 1, Which of the following websites or software applications, are related to e-learning?, , 1, MOODLE, , 2. CoWin, , 3. www.inflibnet.ac.in, , 4. www.egyankosh.ac.in, , A. | and 2, B. 2,3 and 4, C.3 and 4, D. 1,3 and 4, , 2. Which of the following are correct statement(s)?, , 1, Cloud computing allows us to access our resources anytime, by storing them on the ‘cloud’ instead of private computer or, a local server., , 2. DigiLocker is a cloud based platform launched under, Digital India., , 3. Today, mobile phones are capable of providing VoIP, services., , A. | and 2, B. 2 and 3, C. 1 and 3, D. 1, 2 and 3, , Shohaib’s Classes
Page 2 :
NET-JRF TUTORIAL BY MANIPURI YOUNG SCHOLARS, , 3. Assertion (A): An intranet is a private network for sharing, computing resources and information within an organisation., , Reason (R): Intranet is the private version of the internet., , A. Both (A) and (R) are true and (R) is the correct explanation, of (A)., , B. Both (A) and (R) are true but (R) is not the correct, explanation of (A)., , C. (A) is true, but (R) is false., , D. (A) is false, but (R) is true,, , 4. Which of the following are true?, , (a) The acronym USB stands for Unified Serial Bus., (b) Interpreter is faster than compiler., , (c) Bit is the smallest unit of memory., , (d) HTTP is a programming language., , A.a& donly, B.a & b only, C.b &c only, D. c only, , wm, , Shohaib’s Classes
Page 3 :
NET-JRF TUTORIAL BY MANIPURI YOUNG SCHOLARS, , 5. Consider the following statements., , Statement A: The disparity caused by individual’s access or, lack of access to digital technology is called internet, inequality., , Statement B: The problem of access has been a major, downside of emerging technologies., , A. Both statements are true, B. Only statement A is true, C. Only statement B is true, D. None of the statements is true, , 6. Which among the following statements about Read only, Memory (ROM) is incorrect?, , A. It is internal memory., , B. It does not lose its content even when the computer is, turned off., , C. The user can write and read data from ROM., , D. All of the above statements are correct., , Shohaib’s Classes
Page 4 :
NET-JRF TUTORIAL BY MANIPURI YOUNG SCHOLARS, , 7. Match LIST-I and LIST-IL., , , , , , iv. UTP cable, , , , , , LIST-I LIST-II, , i. VoIP a. Uses light pulses to transmit, ii. Fibre optic data, , cable b. Fundamental network, , iii. URL, , identification for any resource, connected to the web, , c. Unshielded Twisted Pair, , d. Technology used for delivery of, voice over the internet, , , , A. i-a, ii-c, iii-d, iv-b, B. i-d, ii-a, iii-b, iv-c, C. i-d, li-c, ili-a, iv-b, D. i-c, ii-d, iti-b, iv-a, , 8. Consider the following statements., 1. A bot is a hardware designed to do certain tasks., 2. Bots are used in DDoS (distributed denial of service), , attack., , Which among above is/are correct?, , A. Only 1, , B. Only 2, , C. Both | and 2, D. Neither | nor 2, , Shohaib’s Classes
Page 5 :
NET-JRF TUTORIAL BY MANIPURI YOUNG SCHOLARS, , 9. March LIST-I and LIST-IL., , , , LIST-I LIST-II, , a. Phishing i. Stealing other’s identity to, b. DDoS cheat on some other persons, c. Spoofing using that stolen identity, , d. Virus, , A. a-iv, b-i, c-iii, d-ii, B. a-iii, b-iv, c-i, d-ii, C.a-i, b-v, c-ii, d-iii, D. a-ii, b-v, c-i, d-iii, , Shohaib’s Classes, , , , ii, Stealing other person’s, sensitive information by, disguising as a trustworthy, individual, , iii. Capability to spy upon, others, , iv. Keeping a system under, siege, , v. Crashing of web servers by, illegitimate clients